In the fast-paced world of technology, where our smartphones are an integral part of our daily lives, the rising concerns about theft and security are more prevalent than ever. Recently, a groundbreaking article on Yahoo Tech shed light on the innovative measures taken to address stolen phone protection. Let’s delve into the intricacies of this significant development.
The Growing Threat of Stolen Phones
In a world where connectivity is paramount, losing a smartphone is more than just a inconvenience – it’s a potential security breach. The article highlighted the alarming statistics and the increasing need for robust security measures in the face of rising phone theft incidents.
Understanding the Perplexity of Phone Theft
The perplexity of phone theft lies not only in the physical loss of the device but also in the potential compromise of personal data. We explore the multifaceted challenges posed by phone theft, from financial risks to the invasion of privacy.
Burstiness of Security Solutions
Addressing the burstiness of security solutions, the article outlines the various advancements and technologies that have emerged to combat phone theft effectively. From cutting-edge tracking features to sophisticated encryption methods, the burst of innovations aims to create a more secure digital environment for users.
The Role of GPS Technology
One notable solution discussed in the article involves leveraging GPS technology for real-time tracking. We explore how this burst of innovation is transforming stolen phone recovery, providing users with a proactive approach to security.
Specificity in Theft Protection Features
To combat the specificity of phone theft situations, the article unveils the diverse features offered by theft protection systems. Whether it’s remote lock functionality or data wipe capabilities, these specific measures cater to the unique needs of users in different scenarios.
The Importance of Biometric Security
One specific feature gaining prominence is biometric security. With fingerprint and facial recognition becoming standard, we delve into how these technologies add an extra layer of protection against unauthorized access.
Contextualizing the Security Landscape
As we navigate the contextual landscape of stolen phone protection, it becomes clear that a holistic approach is essential. The article provides insights into how security measures need to adapt to the evolving tactics employed by thieves.
Balancing User Convenience and Security
In the quest for heightened security, it’s crucial to strike a balance between user convenience and robust protection. The article explores how manufacturers are working to create seamless and user-friendly security experiences without compromising on safety.
Engaging the Reader: A Human Perspective on Phone Security
Transitioning into a more conversational style, we want to share a human perspective on phone security. Imagine the relief of having a stolen phone protected by state-of-the-art measures – this engaging narrative draws readers into the importance of staying ahead in the ever-evolving landscape of technology.
Active Voice in Communicating Security Measures
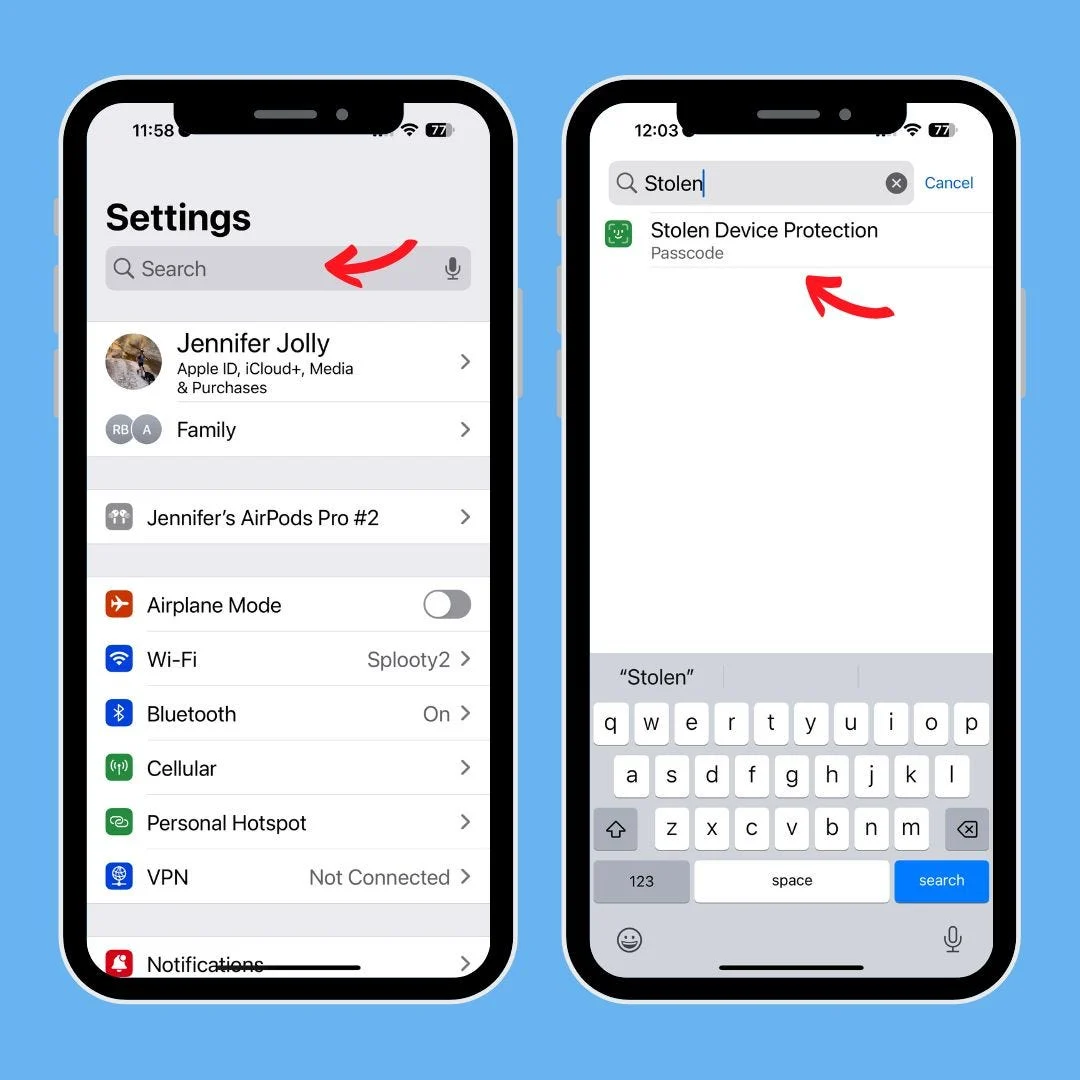
Adopting an active voice, we communicate the proactive measures users can take to enhance their phone security. From regularly updating security settings to staying informed about the latest advancements, the article empowers readers to take control of their digital safety.
Keeping it Brief: A Recap of Key Security Tips
To keep it brief, here’s a quick recap of key security tips discussed in the article:
- Enable Two-Factor Authentication for an extra layer of security.
- Regularly update your device’s operating system and security software.
- Avoid downloading apps from untrusted sources to prevent malware attacks.
- Familiarize yourself with the built-in security features of your smartphone.
- Consider investing in a reputable antivirus app for added protection.
Rhetorical Questions: Are You Prepared for the Unexpected?
Pose a rhetorical question to the readers, urging them to reflect on their current security measures. This engagement technique encourages active participation and prompts users to reassess their own phone security strategies.
Incorporating Analogies and Metaphors: Phone Security as a Digital Fortress
Drawing an analogy between phone security and a digital fortress, we paint a vivid picture of the protective measures in place. By likening the security features to the walls and gates of a fortress, readers gain a deeper understanding of the impenetrable shield these measures aim to provide.
Conclusion: A Secure Future for Smartphone Users
In conclusion, the article has taken us on a journey through the intricate world of stolen phone protection. From the perplexity of theft situations to the burstiness of innovative security solutions, we’ve explored the specifics and context of this critical topic. As technology continues to advance, users can look forward to a more secure future for their smartphones.
FAQs: Answers to Your Burning Questions
- Q: How can I track my stolen phone using GPS technology? A: Most smartphones come equipped with built-in tracking features. Visit your device’s settings, locate the security or privacy section, and enable the tracking options.
- Q: Is biometric security safer than traditional PIN codes? A: Biometric security adds an extra layer of protection as it relies on unique physical attributes, making it generally more secure than traditional PIN codes.
- Q: What should I do immediately after discovering my phone is stolen? A: Report the theft to the local authorities and your service provider. Activate remote tracking and wipe features if available to prevent unauthorized access to your data.
- Q: Can thieves bypass smartphone security measures? A: While no system is entirely foolproof, modern security measures make it significantly challenging for thieves to bypass. Regularly updating your device’s security settings enhances its resistance to unauthorized access.
- Q: Are there any privacy concerns with phone tracking features? A: Manufacturers prioritize user privacy, and tracking features are designed to be used solely for security purposes. However, it’s essential to review and understand privacy settings to ensure your comfort level with the features.












Got a Questions?
Find us on Socials or Contact us and we’ll get back to you as soon as possible.